Subtotal 0 €
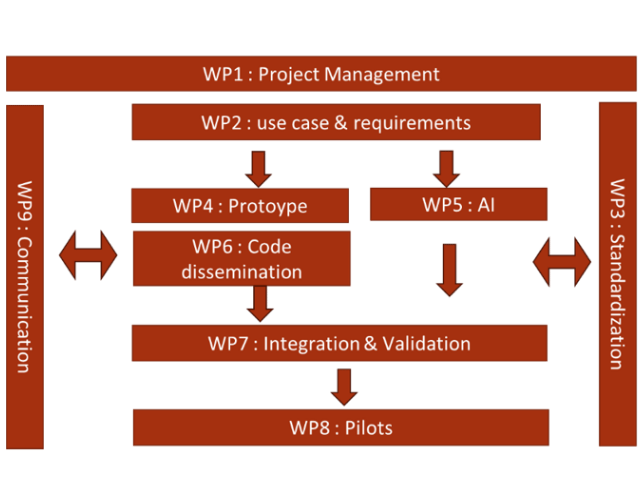
The overall Safe4Soc project is composed of nine work-packages:
The project has two milestones:
All work-packages share the same two milestones. However, these milestones are composite. The description of the milestone and the means of verification have been adapted to each workpackage, to ensure that the project will meet its objectives across all work-packages.
Coordinator – Institut Mines-Telecom (IMT)
Participants - All
The aim of WP1 is to manage the project to time and budget; to co-ordinate the activities; to monitor and adjust the implementation plan if necessary; to monitor the data management and the ethics.
The following tasks are set:
Deliverables:
Coordinator – Fraunhofer Institute for Applied and Integrated Security AISEC (FHG)
Participants - IMT, CEA, EHT, NRD, CSI, NIC, TLB, VIC, VMU.
The objective of WP2 is to define the use cases as well as the overall requirements.
The following tasks are set:
Deliverables:
Coordinator – Institut Mines-Telecom (IMT)
Participants – FHG, EHT, NIC, NRD, CSI, VIC, CEA, TLB, VMU
The objective of WP3 is to align IDMEFv2 format with cross border SOCs needs and to achieve its standardization.
The following tasks are set:
Deliverables:
The three major deliverables of WP3 are the three drafts/RFC (format, transport and BCP) and will be directly published on IETF website.
Coordinator – EHT
Participants – FHG, NIC, TLB, IMT, NRD, CEA, TLB.
The objective of the WP4 is to develop and publish IDMEFv2 open-source tools and preprod SIEM prototype. The development of the open-source SIEM has multiple objectives. a) it will help validate the theory of IDMEFv2 with real implementation , b) it will serve as “running code” for IETF to prove the format is useable, c) it will be used on WP7 for the simulator and WP8 for the pilots and d) by being published as open-source it will promote the format and strengthened the dissemination.
The following tasks are set:
All the code and programs developed in WP4 will be published with open-source licence on the project GitHub and these publications will be announced through the project communication medias (website, mailing list, social network, etc). The SIEM tools will re-used existing open-source SIEM component but will be adapted to state-of-art technologies: Kakfa broker for the alerts transport, NoSQL database storage, web 4.0 interface, Logstash parsing for the logs, etc.
Deliverables:
Coordinator – French Alternative Energies and Atomic Energy Commission (CEA)
Participants - VIC, VMU, IMT.
The goal of WP5 is twofold:
The following tasks are set:
1) identification and collection of relevant raw hardware data from embedded systems (HPC, syscalls, etc.);
2) structuration of raw data using existing tools to obtain table-like structured data;
3) construction of relevant graphs;
4) AI/ML models on graph and heterogeneous data to assess link or node threat level. Several data sources (e.g.process,system, network) may be initially processed separately.
1) How to convert a detected threat from 5.1 to an IDMEFv2 message describing the threat, possibly including additional information generated by AI/ML. Several messages may also be used if multiple stages are involved;
2) How to use incoming IDMEFv2 messages to identify possibly related events in a separate data source or at another SOC. A preliminary step will be to use the IDMEFv2 message to identify the threat and the related events in the original data source (log, message, channel) from the SOC emitting the IDMEFv2 alert. An underlying goal of the task is to provide feedback regarding what data to include in the IDMEFv2 format to get the most out of the AI/ML tools, while making sure that the shared data respect ethics and do not cause unintended harm. This implies being responsible about respecting the privacy of users and not disclosing sensitive information.
Deliverables:
Coordinator – TECLIB (TLB)
Participants – IMT, EHT, NRD
The WP6 is responsible of IDMEFv2 dissemination through the open-source community and compatibility with commercial software.
The following tasks are set:
Deliverables:
Coordinator – The French Alternative Energies and Atomic Energy Commission (CEA)
Participants - NIC, TLB, FHG, IMT, CSI, EHT, NRD, VMU
WP7 is responsible of the integration and validation of WP4, WP5 and WP6 development. The tools will be integrated together and validation will be run through simulation.
The following tasks are set:
Deliverables:
Coordinator – EHT
Participants – IMT, CEA, FHG, NRD, CSI, NIC, TLB, VIC, VMU
The aim of WP8 is to deploy and run the SAFE4SOC prototype developed in WP4, WP5 and WP6 in real conditions, as close as possible to the live working environments used in the production of SOCs. To be realistic, the validation will be planned, organised and conducted taking into account constraints and requirements of involved SOCs in terms of technologies (tools used such as SIEM, SOAR, etc.), processes (alerts triages, normal and emergency conditions, etc.) as well as policies and regulations (e.g. service level agreements with SOC customers, compliance with standards such as ISO27001,ISO27005, etc.). The validation will test the effectiveness and the efficiency of the solution on live data while adhering to safety and integrity of the data inside each SOC. The analysis of the validation results will identify strengths, weaknesses, opportunities of improvements and threats that will allow the consortium to improve the proposed standard and the prototype implementation, as well as to be used as valuable input for the refinement of the SAFE4SOC exploitation plan and activities.
The following tasks are set:
Deliverables:
Coordinator – Vytautas Magnus University (VMU)
Participants - All
The primary objective of WP9 is to effectively disseminate and exploit the outcomes of the project to all relevant stakeholders, encompassing SoC providers and users (public and private), R&D providers for SoC, CyberRange operators, regulators, national agencies, policy stakeholders, local and regional educational organizations, and the general public.
This objective is undertaken with the purpose of maximizing the expected impact and boosting the project sustainability for the continuation of the project after the EU-funding. Extensive communication, dissemination, and exploitation will be accomplished through various activities, including:
In order to accomplish the objectives outlined in the CDE plan, a variety of activities will be implemented. These include establishing and managing a dedicated website for the project, utilizing social networks, producing newsletters, publishing articles, producing video material, organizing engagement and networking activities, participating in exhibitions or conferences, and hosting project events.
The following tasks are set:
Deliverables: